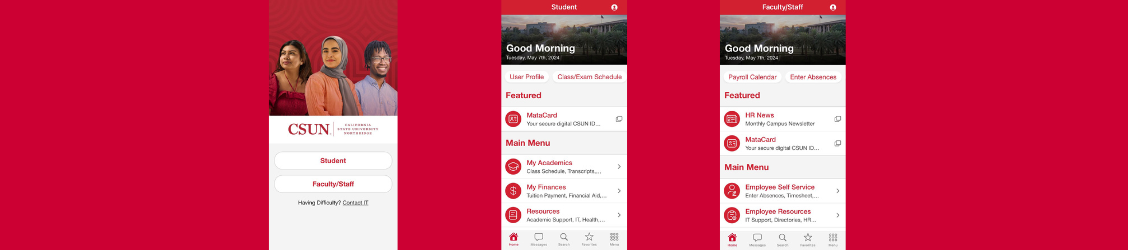
The CSUN app has been redesigned!

Academic Continuity

Welcome, Canvas Ally!

Stay Connected!

Take your files with you
Protect yourself!

Learn anytime. Anywhere.

MATLAB

Anytime access to select software

Have you installed MS Office?

Ready, Set, Zoom!

Protect yourself!

Have you heard about this fellowship?
Information Security is a department within the division of Information Technology at California State University, Northridge. The department is responsible for implementing and maintaining campus-wide security policies and standards. Services provided by Information Security include Security Awareness Training, Breach & Incident Investigations, Vulnerability Assessments, and Risk Assessments. A major role of the department is to educate and advise campus faculty, staff, and students of the risks to the data.
For detailed information on services provided, please refer to the resources below or contact Information Security at (818) 677-6100.
Information Security Bulletin
Critical iOS fixes - Patch your Apple Devices Now (12/2/23)
Apple has released iOS 17.1.2, along with a warning to update now. iOS 17.1.2 fixes two iPhone security flaws—both of which are already being used in real-life attacks.There is also an update to MacOS and Safari for older Macs. Here is the link to the Apple Security Page.
Malicious Google Ads
Beware of a sophisticated cyber threat known as SEO#LURKER! Cybersecurity experts have uncovered a malicious scheme targeting users searching for WinSCP. Attackers manipulate search results and Google ads to lure unsuspecting individuals into downloading malware instead of legitimate software. These deceptive ads redirect to compromised websites, leading to a fake WinSCP site where a seemingly genuine installer hides malicious Python scripts. Victims, particularly in the U.S., are targeted through geoblocking. This tactic isn't new; similar attacks have targeted PyCharm users.
Need tips on how to avoid Malicious Google Ads? Please visit our Security Blogs website.
CSUN Students Targeted With Phishing Emails
CSUN students receive many emails through their student email everyday. With there being so many emails, it can be easy to accidentally open a phishing email and compromise your data on your device. A phishing emails is a scam attackers use to deceive people into revealing sensitive data or to install malware such as ransomware. For an example of what a phishing email looks like, please visit this link. If you have received a phishing email or have any questions please contact the Information Security team at iso@csun.edu
Ransomware
Ransomware is a type of malware that prevents or limits users from accessing their system, either by locking the system's screen or by locking the users' files unless a ransom is paid. More modern ransomware families, collectively categorized as crypto-ransomware, encrypt certain file types on infected systems and forces users to pay the ransom through certain online payment methods to get a decrypt key. Ransomware can be installed through deceptive links in an email message, instant message or website. Ransomware remains a resilient, lucrative form of attack for hackers and shows no signs of slowing. CSUN, being a large organization with many users, is vulnerable to these types of attacked considering ransomware affects over 72% of organizations worldwide. If you have fallen victim to a Ransomware attack or have any questions please contact the Information Security team at
Report all Zoom-bombing events
It is extremely important that all Zoombombing events are reported so they can be investigated.
Report the event!
If someone bombs your meeting please report the event immediately. Send an email to iso@csun.edu and provide
- Your name and email address
- The date and time of the meeting
- The Zoom link and the meeting ID number
- The name of your course and (anything else like Course #)
- Describe what happened in as much detail as possible
Need tips on how to avoid Zoombombing? Please visit How To Keep Your Zoom Sessions Secure.
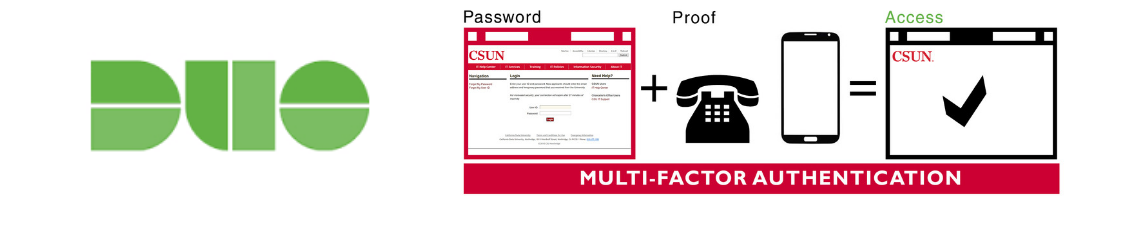
Information Security Guidelines For Working from Home
Why Working Remotely is Different
Working at home presents a unique challenge for information security because remote work environments don't usually have the same safeguards as working in the CSUN environment. When CSUN faculty and staff are on the CSUN campus, they are working behind layers of preventive security controls. While not 100% foolproof, it is harder to make a security mistake while in the CSUN environment. However, when a CSUN issued device leaves the perimeter or faculty and staff work remotely, new risks arise and additional protections are essential.
Threats to Working Remotely
Unsecured Wi-Fi networks: Not everyone has a secure home network with strong firewalls. Public Wi-Fi networks, such as those in coffee shops, are also unsafe for conducting business. Unsecured public Wi-Fi networks are prime spots for malicious parties to spy on internet traffic and collect confidential information.
Need Help with Information Security?
Contact the Office of Information Security at (818) 677-6100. To report incidents of abuse, send an email to abuse@csun.edu or: